IIS 6: Setting up SSL - Overview
31 January 2011 • by Bob • IIS
Many years ago I wrote a series of instructions that used dozens of screenshots in order to show my coworkers how to set up and enable Secure Sockets Layer (SSL) communications in IIS 5, which I eventually turned into a blog series on one of my personal blog sites. A few years later I wrote a sequel to that series of instructions for my coworkers, and I wanted to turn that into a series of walkthroughs in the IIS.net website. Sometime ago I proposed the idea to Pete Harris, who was in charge of IIS.net at the time, but then I changed jobs and we scrapped the idea. We followed up on the idea a short time ago, but we just couldn't find a place where it made sense to host it on IIS.net, so Pete suggested that I turn it into another blog series. With that in mind, over a series of several blog entries I will show how to configure SSL on IIS 6.
Note: This first post will leverage a lot of the content from the overview that I wrote for my IIS 5 blog series, but subsequent posts will reflect the changes in IIS 6.
Much like IIS 5, setting up SSL on IIS 6 is pretty simple. SSL is a Public Key/Private Key technology, and setting up SSL is essentially obtaining a Public Key from a trusted organization. The basic process for working with SSL is reduced to the following actions:
- Creating a Certificate Request
- Obtaining a Certificate from a Certificate Authority
- Installing the Certificate
While not necessary, installing certificate services on your computer is helpful when troubleshooting SSL issues, and I'll discuss that later in this blog series.
Creating a Certificate Request
This is a series of steps that need to be performed on the web server, and they differ widely depending on the server and version. A web administrator is required to enter information about their organization, their locality, etc. This information will be used to validate the requester.
Obtaining a Certificate from a Certificate Authority
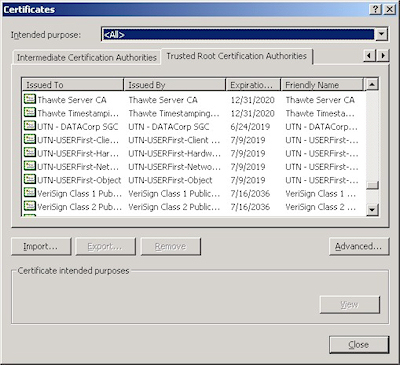
This is when a web administrator submits their request for a certificate to a Certificate Authority (CA), which is a trusted organization like VeriSign or Thawte. For a list of trusted organizations, see the following section in Internet Explorer.
You can choose to trust a new CA by obtaining the Root Certificate from the CA. (I'll post an Obtaining a Root Certificate blog with more information later.)
Installing the Certificate
After a request has been processed by a CA, the web administrator needs to install the certificate on the web server. Once again, this series of steps needs to be performed on the web server, and the steps differ depending on the web server and version.
For the Future...
In future blogs I'll go through the steps for creating certificate requests, obtaining certificates from a CA, and installing certificates. Following that, I'll discuss setting up a CA for testing SSL in your environment.
Note: This blog was originally posted at http://blogs.msdn.com/robert_mcmurray/
100 Things the 511th Learned During the ARTEP of 1991
30 January 2011 • by Bob • Military
Today's contribution marks the 7th installment in my series about the 511th MI Company's misadventures, which I collected during my tenure there from 1988 through 1991. This list was composed by the EW2 platoon during the ARTEP of 1991 - I believe it was in April - which we dubbed "Operation Pogo Stick." This name seemed apropos because of the considerable frequency that the EW platoons were required to jump sites, for no apparent reason other than the sheer fun of watching the level of aggravation that it caused. I think that this was the last deployment that I went on with the 511th; shortly after the ARTEP had ended, DeGrood and I got our orders to PCS back to the states, and everyone else got orders to Kuwait.
Things we learned during ARTEP '91
- Hot refuels really are (with lanterns).
- Point fire extinguishers at flames.
- Don't play Russian Roulette with a .45.
- Mosquito nets make good kindling.
- Calling SGT Tabbert "Larry" is effective aggravation.
- Being "killed" is the only way to get a couple hours' sleep.
- The Official ARTEP Song: "Jump" by Van Halen.
- There are no weapon mounts on HMMWV bumpers.
- SGT Rice makes a 2LT with a map look good.
- MI-51's radio has a maximum effective range of 100 meters, and MI-52's is about 100 inches.
- You can get away at MOPP 0 in a MOPP 1 environment, until the MAJ sees you.
- Ken be nimble, Ken be lean, Can't jump over the Concertine. He jump high, he jump low. He get caught, down he go.
- TCAE can get tracks to the field, but not back.
- Security isn't.
- Chase vehicles don't.
- The best form of land navigation is a well-informed German.
- An unheated, unlit tent and a pile of BOGINT tapes is an effective TRQ-32 simulator (bring your own paper).
- The latest in EW sleepware is the DA Morris Improved Stealth Tent.
- Mumbly-Peg is easier with the knife unsheathed.
- This was a very well thought out, and carefully planned exercise. NOT!!!
- Mumbly-Pistol is a game as yet untried.
- SGT Cyr relates well with farm animals. ("Moo...")
- Reimers can sham out of anything if he really wants to.
- Germans on holidays make interesting navigational obstacles.
- The TRQ-32 is the coffee-making, radio watch sitting, front seat sleeping, $800,000 car stereo wonder of the 20th century.
- Fred can never be in too warm an environment.
- The TRQ-32 glove box is hell on the shins.
- Handcopying BOGINT in MOPP 3 is a joyous experience.
- It's just no fun wearing a protective mask with a runny nose.
- GRA-39's make excellent car stereo amplifiers.
- TRQ-30 DF antennas are better left in the rear.
- M-8 alarms work better without batteries.
- We can ID more types of static now.
- You can teach the LT something new every day.
- LT's aren't sensitive items, but they have feelings, too.
- The LT wigs out when challenged.
- It was good training. NOT!!!
- Who's the a****** who made those 2-minute intercept to 2-hour static tapes?
- Blind TCAE geeks should not be allowed to recon intercept sites.
- The TACJAM squad is now cross-trained in landscaping.
- Duerksen can "hold it" for 4.5 days.
- Roddick don't know s*** about whoopie lights.
- Menthol cigarettes don't cut it.
- Roddick's new discovery - wet newspaper. It camos as it cleans.
- It's more fun 4-wheeling.
- Starvation is preferable over chili-mac and lima beans.
- Duerksen and Roddick can eat a whole cow.
- German kids love MREs. (That looks bad as a culture, doesn't it?)
- Braddy is too lazy to drive 10 minutes to see us. (So the d*** flew.)
- Germans don't like having M-60s pointed at them.
- Noise discipline need not be observed near 200 decibel generators.
- Propane heaters are heaven.
- Rich is a lying son-of-a-b**** when asked about this ARTEP.
- The CO has no sense of humor where guard posts are concerned.
- O'Conner has no tact.
- The TLQ squad is still the Kase-Camo Net Meisters.
- It seems like you always jump during your sleep shift.
- TCAE goons sleep more in one night than EW geeks do in a whole week.
- Mumbly-Peg doesn't work with swiss army knives.
- Lanterns with broken globes are somewhat dangerous.
- Field coffee isn't.
- Guard duty sucks. (That's why officers don't do it, right?)
- Vehicles, though forbidden, are still the preferred sleeping areas.
- Hooches get simpler the more you jump. ("All I need is a cot...")
- The TACJAM squad knows Germany.
- After a week in the field, even the locals smell good.
- World War II issue maps are not effective navigational tools.
- Only the TLQ squad can out Black-6.
- (This number is still not seen hereabouts.)
- Sure DeGrood has tonsillitis.
- Reimers' other foot will be broken upon our return.
- When you're a minute early on shift you're the greatest, when you're a minute late you're an a******.
- Johnson's magazine subscriptions are enjoyed by all.
- Where's the Jam button?
- Where's the Fix button?
- What freq am I on?
- Are we on Zulu or Local time?
- Mr. Roller is as effective an NBC alarm as an M-8 without batteries.
- Just because it looks like rain doesn't mean that it will.
- You know that you need a haircut when you can grow dreads in the field.
- Brush guards do.
- Brushing your teeth is really a morale booster.
- If German's can find our sites, why can't we?
- Never ask DA for a light. ("But he looks good with a singed face...")
- Burning tents are wonderful reference points at night.
- What do Germans do with all that lumber?
- The TRQ-32 needs a microwave.
- After a week of ARTEP, even TROJAN sounds good.
- The TRQ-32 has the only working radio in the PLT.
- It's nice to pull radio watch in a vehicle with a good heater.
- Cold mornings suck. (1 week from summer.)
- We never thought we'd be so happy to see a 1-week field problem end.
- Duerksen doesn't like grits.
- Groovy man remembers lots of worthless music.
- Everybody still wants to be a jammer.
- MOPP 1 is quite warm.
- Civilian life can't be all that bad.
- Newbies whine almost as much as EW1, but not quite.
- TCAE can drop the ball, duck the issue, pass the buck, and wash their hands of it better than anyone else.
- I wonder what Hohenfels will be like this year...?
In another strange turn of events, after I PCS'd to Fort Huachuca, I met the guy that made those 2-minute intercept to 2-hour static tapes that we mentioned in item #38 of the list, and I wound up working with him. (And just to satisfy anyone's curiosity - yes, he made those on purpose. He was a nice guy, but he had a wicked sense of humor.) Later on, I was asked to create intercept tapes for the MI officer school at Fort Huachuca, and I followed his lead by creating tapes that sounded like HF traffic - with hours and hours of radio printers, static, and morse code transmissions stomping on top of the voice messages. (FYI - The officers hated these tapes - mission accomplished.) But here's a quick behind-the-scenes trivia fact: I didn't actually record any actual radio printer or morse code transmissions from HF frequencies - I created them on my computer. Most radio printer traffic is simple Frequency Shift Key transmissions, so I wrote some algorithms that would allow me to enter a text string into my computer, which would be converted to binary, and then encoded into an audio stream based on a baud rate and space/mark frequencies that I picked. When I was done - they sounded identical to the real thing. So what did all of those ear-splitting radio printer messages actually say if you plugged them into a computer? Things like, "I hate the Army," "I can't wait to ETS," etc. Yes - even then I was a geek.
IHateTheArmy.mp3 (76.73 kb) "I Hate The Army" Frequency Shift Key (FSK) Sample
Famous 511th Quotations from Hohenfels 1990
29 January 2011 • by Bob • Military
In the 6th part of my series on the 511th MI Company, I have a short list of quotes that the ESM guys collected at Hohenfels, 1990.
- "Don't [dip] chew when expecting chow; it always arrives in 2 minutes." - D.A. Morris
- "Sorry, I used the wrong grid." - Bill McCollum
- "So, this is where we are...?" - Jeff Norris
- "I wish I were an Oscar Meyer Wiener." - Joe Masten
- "You guys aren't Prima Donnas!" - 1LT Innocenti
- "You talk a lot of s***, but you're just another officer." - Fred
- "More follows..." - CPT Quinn
- "Who's f***in' around, dammit?!!" - J. Morris
- "I'll either make a career in or out of the Army." - Jeff Norris
- "F*** the camo nets..." - EW2's ESM squad
- "Slow that thing down or I'll have you force-marching everywhere!" - CPT Quinn
- "Are we doing the speed limit?" - 1LT Innocenti
- "This is good training." - LTG Joulwan
- "It's hard to convince Fred that he's wrong." - Whitfield
- "I'm not wrong!" - Fred
- "That's the problem with NCO's..." - Felix
- "The 511th MI Company thanks you for that grid..." - Steve Barnes
- "You have to go to MOPP4? I hate it when that happens!" - Dork
Ah, CPT Quinn - everyone tried to explain to him that "break" was the proper proword to use when you had more to send over the radio, but he steadfastly refused to use anything other than "more follows." Obviously CPT Quinn was trained incorrectly when he went through MI Officer Basic. In one of those weird full circle coincidences, when I transferred to Fort Huachuca the following year, I wound up being the NCO that was in charge of training and grading the officers that were going through MI Officer Basic. I had no qualms whatsoever about telling any officer that they were a "NOGO" at my station, because I knew that these officers were going to wind up in charge of some poor MI platoon, and I couldn't put my fellow MI brethren through the embarrassment of having an officer that didn't know how to use the darn radio correctly.
1LT Innocenti and I did not get along on this field problem - although I don't think that he got along with anyone else in the EW platoons. Since 1LT Innocenti moved to GSR immediately after we returned to garrison, we only had him as a platoon leader for the combined duration of Hohenfels and Grafenwoehr, or about six weeks total, making that one of the shortest durations for a platoon leader that I saw in my eight years of military service. D.A. Morris saved my career while we were out in the field at Hohenfels when I stepped towards 1LT Innocenti with the full intention of decking him after he refused to let D.A. and I take everyone's guard duty and radio watch shifts to make up for all their hard work over the past several weeks. 1LT Innocenti claimed that he had done more work than anyone else, while in reality the only duty that he performed was running chow for us when he wasn't sleeping. What was even worse, his poor choices for words were accusing all of my subordinates of being lazy, while in reality they had been working nearly round-the-clock for several days. This was too much for me to take, so my right arm clenched into a fist and it would have been travelling in the direction of 1LT Innocenti's face when D.A. caught my arm and pulled me aside. I found out later that 1LT Innocenti had a black belt in Karate - so I probably wouldn't have been able to land a single punch before being hauled away to prison for assaulting an officer. (Thanks D.A. for saving my life!)
I bumped into CPT Innocenti several years later when he was going through the MI Officer Advanced Course in Ft. Huachuca, where I was helping to teach MI Operations. By that time we were able to have a few laughs about our shared history with no hard feelings. (CPT Innocenti - if you ever read this, my apologies once again; I was pretty young at the time.)
Another funny story about Hohenfels in 1990 was that I was one of only a handful of people that were chosen from the 11th ACR to brief LTG Joulwan, (who was the commanding general for all of the US Army forces in Europe), about regimental operations in Hohenfels. When the general arrived, I gave him a tour of the ESM gear, showed him how it worked, explained how we conducted operations, etc. After fifteen minutes or so, LTG Joulwan asked me what I thought of his field problem. I looked him right in the eye and said, "Frankly sir, I think it sucks." At that moment, 1LT Innocenti was standing behind the general, and I watched as he put his face in his hands - probably feeling that his career had just ended. The general was momentarily taken aback, and then he asked, "Why?" So I took the next five to ten minutes or so explaining how his deployment of US forces didn't match actual enemy tactics, how their radio communications were completely dissimilar, how we were able to wreak havoc simply by ICD'ing everyone on the planet, etc. The general and I had a pretty good conversation that lasted for several minutes, and eventually we agreed to disagree on several points. Before his departure, LTG Joulwan gave me one of his custom-made USAEUR coins "in recognition of my outstanding achievements," then he got in his humvee and drove off. CPT Quinn dropped by later and informed me that out of the hundreds of people that LTG Joulwan had met that day, I was one of only two people to which the general had given a coin. (CPT Quinn also asked me never to do that again.) So I like to remember that I received a medal (more or less) for being one of the few people who was willing to tell a three-star general to his face that I thought his training sucked.
More Famous Moments in the 511th History
27 January 2011 • by Bob • Military
My 5th installment of this series about the 511th MI Company is pretty much a sequel to the 4th installment. I'm fairly certain that I had two lists in my notes because they were more than likely created during different field problems a year or so apart.
It was also a great day for the 511th when...
- Alex hits a lady's car to get a date, totals the car, and doesn't get the date (Reforger, 1990)
- 10-Pin walked into an enemy HQ and asked for their crypto fills, and he got them (Hohenfels, 1989)
- Alex was relieved as platoon sergeant for EW2, and got a better job in the process (February, 1990)
- Babs gets lost in Augsburg with his prized possession; his 1:100,000 scale map (Reforger, 1990)
- Felix screamed at OCE's he thought were attacking while he was [relieving himself] in the bushes (Hohenfels, 1990)
- The Tacjam went down for the count (Reforger, 1990)
- The TRQ-32 team loses 5 people to a 10th Mountain suicide squad, but still manages to kill the whole squad (Reforger, 1990)
- Romero and Meador rolled MI-28 when their brakes failed (Hohenfels, 1990)
- Nada picks a fight with a wall in the Tacjam, and loses (Reforger, 1990)
- J.J. qualifies on the M16, on the 198th round fired (Grafenwoehr, 1990)
- Alex ordered Whitfield to be thrown into the mud pit for taking a shower while everyone else was unloading vehicles in the MOPO (Caravan Guard, 1989)
- Dodge hits himself in the head with his M16 getting out of a HMMWV (2 minutes after Reforger, 1990)
- Someone threw up all over the Bay of Pigs at Mt. Meissner, but no one ever found out who (November, 1989)
- Martin and Dodge ICD'd a Medevac net, a little too successfully (Reforger, 1990)
- D.A. becomes a BOGINT Master (Sudden Eudy, 1989)
- Mason asked Cyr for a can to [relieve himself] in, then asked Cyr to dump it for him (Reforger, 1990)
- D.A. got a date! (March 1, 1990)
- Fred made a mistake on the TRQ-32 (Hohenfels, 1990)
- EW2's ECM squad ambushed the ESM squad and no one cared enough to get out of bed (Hohenfels, 1990)
I should like to point out that the mistake that I made on the TRQ-32 was not opening the ventilation flap on the side of the generator. I pointed that out myself, but that didn't stop the rest of the squad from holding me down and giving me a pink belly. I believe D.A. was the overall ringleader for my punishment, but I'm sure that I had it coming. ;-]
Famous Moments in the 511th History
26 January 2011 • by Bob • Military
In the 4th installment of this series about the 511th MI Company, I have a list of what we thought were great moments in 511th history. I don't know if anyone else recalls, but whenever morale was hitting a low point during a field problem - I'd pull out a pad of paper and have everyone make an obnoxious list of some sort. These lists were usually laced with a great deal of cynicism - and more often than not a great deal of profanity. So I'll have to clean these up a little before posting. ;-]
It was a great day for the 511th when...
- Sarge took a mud bath (O-Day, 1989)
- J.D.'s guitar was destroyed by J.J.
- Caudill threw his computer out the barracks window, then jumped out the window after it and jumped up and down on it (1988)
- Dodge got stuck in the turnstile at Mt. Meissner
- Cyr was attacked in the Snow Bear Pit (November, 1988)
- Punky took a swing at Duncan
- Fred took a swing at Duncan
- Anybody else took a swing at Duncan
- Ortiz rolled MI-40 four times (RTCE, 1989)
- TCAE's tent caught fire (Wildflecken, 1989)
- Punky and Fred slid down Meissner in a GLQ-3B (February, 1988)
- Duncan and Skip got thrown out of Wobeck (February, 1988)
- 1SG Ross went to the field the first and last time (Reforger, 1987)
- J.J. called 1LT Stahl a geek at the Irish Pub
- Cyr and 2LT Gibson got lost in Turkey (Ally Express, 1988)
- 10-Pin sicked his dog, Presely, on Paski (Pre-Artep, 1989)
- Paski got stung by a bee (RTCE, 1989)
- Skip and Duncan threw Felix in the shower
- A waitress told Punky that she didn't speak English after he ordered in German (TRQ-32 TNG, 1988)
- A recon patrol suprised Babbs and scared him to death (Caravan Guard, 1989)
- Skip got beat up by a group of drunk germans at FLTCE
- Whitfield went to the field without a sleeping bag (Bold Lancer, 1989)
- Whitfield went to the field with only one uniform (Caravan Guard, 1989)
- Heave came back from FLTCE with lower scores than he went there with
- Duncan threw up blood at the Kreuz Club
- EW1 was thrown out of a Turkish brothel (Ally Express, 1989)
- Dodge, J.J., Nada, and Stayszyk got drunk and [did something foul] on SGT Berger's truck
- CPT MacDonald threw SSG Alexander off the radio the first time (Caravan Guard, 1989)
- CPT MacDonald threw SSG Alexander off the radio the second time (Reforger, 1990)
- Duncan's car broke down on the way to Meissner, and Degrood wouldn't stop for him
- Dexter got his clearance and lost it in the same weekend
- Lay taught a group of drunk Brits how to rap (RTCE, 1988)
- The Tacjam rolled out of the MOPO
- EW2 helped a German farmer chase his cows (Caravan Guard, 1989)
- EW was QRC'd and didn't find a single freq (Ghost Chaser, 1988)
- Duncan asked why he didn't get a Good Conduct Medal
- J.J. made Duncan clean his bathroom to use his Nintendo
- CPT Stahl left
- The Commo platoon, despite a great deal of cheating, lost to EW2 (O-Day, 1989)
- Paski was promoted to SPC and faced the "Gauntlet"
- Smith, Fred, and Martin stole Whitfield's clothes from the shower room at Mt. Meissner
- 1LT McNeil pulled a bayonet on a group of would-be kidnappers (RTCE, 1989)
- Martin and Fred attacked Hjerrild with pillows at Meissner
- Woolery slipped on black ice when going up to be promoted and hit MAJ Bute
- SSG Valier couldn't pronounce "Patriotism" ("Potatochism!")
Bryant - I'd like to apologize on behalf of Smith, Martin, and myself for stealing your clothes at Mt. Meissner. :-S
I'd also like to state - both emphatically and for the record - that I was a member of EW2 when EW1 was thrown out of the Turkish brothel. :-O
And it would be a great disservice if I didn't point out that there's no way that Cyr would have been lost in Turkey if it had not been for 2LT Gibson - the age old adage that the only thing more dangerous than a 2LT with a gun is a 2LT with a map certainly applies to that situation.
Famous Quotations of the Fighting 511th
24 January 2011 • by Bob • Military
In part 3 of this series about the 511th MI Company, we'll take a look at some common quotes that were said by several members of the 511th, although this list is obviously not exhaustive. These particular phrases were compiled by members of the EW platoons during one of our field problems, although it's been so many years I don't recall which one. ;-]
- "Not!" - J.J. Simmons
- (Anything J.J. says) - Dave Dodge
- "Figure the odds..." - Tim "Sarge" Meador
- "Easy Psycho" - Scott Smith
- "I've gotta go get the mail" - Frank "Skip" Walker (Whenever work needs to be done)
- "Want to hear a joke? Skip." - James Leamon
- "Well, back on the farm..." - Steve Myers
- "Why is everybody always picking on me?" - Bryant Whitfield (and Charlie Brown)
- "Fred, why haven't you made the coffee yet?" - SGT Morris or SGT Alexander
- "But I don't know my telephone number..." - Rich Aylward
- "This ain't Puerto Rico, Mother @#$%!" - Daniel Nadalaliciea
- "Questions? Comments? War stories?" - LTC Harry K. Lesser
- "Hey Stud!" - CPT MacDonald
- "Punky, you're a failure!" - Duncan Habberly
- "You're right." - James "Punky" Brewster
- "Sup wi dat?" - Larry Blanco
- "Hey Guys!" - Tom Haldeman
- "What's up?" - Alvin Heggie
- "Son of a biscuit eater!" - Dave Paski
- "Listen Geek..." - Bob "Fred" McMurray
- "Word" - J.J. Simmons
- "Did you ever see...(any war movie)?" - SGT D.A. Morris
- "Hey, hey, hey." - Breck Tarr
- "C'mere" - Danny Browning
- "Good stuff." - 1LT Stahl
- "Listen Specialist..." - Bill "SGT" Magan
- "That's special." - Ray Neuharth
- "Thank you, Luigi." - Jerome Robinson
- "Omygod! Omygod! Omygod!" - 1LT Babakan
- "Easy..." - Van Cleave
- "Listen buttface..." - Dave Paski
- "Grow up guys!" - Scott Smith
- "Where's chow?" - SGT Alexander
- "Holy Cow!" - Steve Myers
- "What's up?" - Raul Villareal
- "Don't ask ME!" - Anyone who can get away with it
- "Cool points." - 1LT Stahl
- "But SGT Morris..." - 1LT Innocenti
- "What? Huh?" - Larry Blanco
- "Why?" - Johann "Bahn" Hoff
- "More Follows..." - CPT Quinn
For the future, I have some great lists of famous moments in 511th history, and famous quotations from Hohenfels 1990.
Famous Nicknames of the Fighting 511th
23 January 2011 • by Bob • Military
In part 2 of my series on the 511th MI Company, we'll take a look at some of the nicknames from the 511th that I managed to write down; although I need to stick to my disclaimer that I did not come up with these nicknames - I just took the time to write them down. ;-]
- Captain Caveman - Tim Leavitt
- 10 Pin - Bobby Thanepohn
- Sleazer - Jim Leamon
- Punky - Jim Brewster
- Shaggy, Eugene, and J.J. Not - John Simmons
- Ichabod and Felix - Steve Myers
- Tick - Jim Titkemeyer
- Sarge - Tim Meador
- Schone Frau - Dave Young
- Witless and Grimmace - Bryant Whitfield
- Honkytonk Man - D.A. Morris
- The Duke - Danny Browning
- Heave - Steve Maurer
- Maull and Knoore - Terry Knaul and Tim Moore
- J.D. - John Davis
- Fred and Ernie - Bob McMurray
- Eggdod - Dave Dodge
- Skip - Frank Walker
- Lick and Snaggle Tooth - Rick Irvine
- Van Cheese - Kyle Van Cleave
- Michelin Man, Uncle Fester, Bleu Cheese, and Sta-Puf - Steve Terry
- Degrudge - Dave Degrood
- Mr. Peabody and Mr. Maturity - Scott Smith
- Buffalo Bill - Bill Magan
- The Pegster and Heggster - Alvin Heggie
- Burt - Ramon Ortiz
- Oreo Cookie Man, Roly-Poly and Karlik - Dan Onstead
- Splugie - Eudy
- Hanker - Kent Hawks
- Spaski - Dave Paski
- Nada - Daniel Nadalalicea
- Bhudda - Jeff Morris
- Snorris - Jeff Norris
- Roj - Roger Jordan
- Haystacks - Steve Calhoun
- Bahn - Johann Hoff
- Beaver - 1LT Innocenti
- Uncle Martin - Ken Martin
- Dork - Heath Duerksen
- The Three Amigos - Paski, Fred, and J.J.
- The Fat Boys - Duncan, Skip, and Leamon
- The Three Stooges - Felix, Blanco, and Whitfield
- Bullseye Babbs - 1LT Babakan
- Alfalfa - Rich Aylward
- Spanky - 1LT McNeil
- Darla - Some female 1LT from the 108th that 1LT McNeil was chasing
- LT Stahl and D.A.T. - CPT Stahl
- Don Knots - 1SG Hall
- Smelvin - 1SG Ross
- Chief - CW2 Klebo
- Harry K. - LTC Lesser
- Neily D. - MAJ Bute
- Quinn the Eskimo - MAJ Quinn
- Frank or Bob - Richard Lebron
And my personal favorite:
- The Evil Lord Torak - CW2 Torak
There is one nickname that I wrote down that I didn't post here, and that was for Bill McCollum. I didn't add his nickname to this list because it might not be fit for the public. If you remember his nickname, you can smile about it now. If you don't, that'll remain a secret between the rest of us.
Who did I miss?
10/21/2014 Update - Bullseye Babbs was a 1LT who took over one of the EW platoons. He earned his nickname on one of the M-60 ranges when he failed to understand how his weapon's scopes worked, so instead of throwing rounds 1km downrange like everyone else, he was thoroughly pulverizing the ground about 5-10 feet in front of us; huge amounts of debris were being thrown into the air as everyone was screaming at him to cease fire. (It probably would have been funny if it hadn't been so dangerous.)
03/14/2018 Update - Terry Knaul dropped me a line to let me know that I had his name listed incorrectly; my apologies, and that has been fixed.
Famous Callsigns of the Fighting 511th
22 January 2011 • by Bob • Military
Over the 3.5 years that I spent in the Fulda Gap with the 511th MI Company, I collected and saved a lot of the stories and lists that the EW and TCAE teams put together. All of this nostalgic trivia is twenty years old now, but it still makes me laugh when I think about the people and times that it represents. Of course, this is mostly a collection of inside jokes with the people that were there.
So this will be part one of a series, and I should point out that I did not create this information - I just took the time to write it down. ;-]
- Bleu Cheese - Steve Terry
- Red Chief - Chief Klebo
- Red Stool - Alvin Heggie (With a case of local sickness in Turkey)
- White Spank - Lt. McNiel
- Blue Babs - Lt. Babakan
- Blue Lips - Dan Nadalalicea (aka Davy Crockett)
- Blue Popeye - David Alexander
- Snow White - Dave Paski
- Black Sheep, Blue Honk, or Blue Mustang - D.A. Morris
- The D.J. - Mike Tabbert
- Blue Grimmace - Bryant Whitfield
- Blue Shag - J.J. Simmons
- White Duke - Danny Browning
- Blue Ears - Dave Degrood
- Blue Alf - Rich Aylward
- Blue Geek - Bob "Fred" McMurray
- White Whine - Scott Smith
- Red Whine - Jeff Norris
- The Wacky World of Cartoon Characters - The 511th Jammers
- Blue Bahn - Johan Hoff
- Blue Beaver - 1LT Innocenti
UPDATE: While these were not entirely unique, we often used the following color-coded generic callsigns when we were on recon assignments where only one radio entity was present from each of the different platoons:
- Whitesnake
- Black Sabbath
- Red Rider
- Blue Oyster Cult
Killer Rabbits from Antiquity
07 January 2011 • by Bob • Humor
For those of you who thought that the killer rabbit in Monty Python's "Holy Grail" was a work of fiction, I suggest that you see the top center pane in this stained glass detail from the West Rose Window of Notre Dame in Paris. Apparently brutal bunnies must have been an issue when the French built this cathedral, or perhaps the French will run away from anything.
(Note: Giving credit where it is due, this image is originally from the web page at La Cathédrale Notre Dame de Paris.)

Replacing a Military Radio - The Hard Way
04 January 2011 • by Bob • Humor, Military
Many years ago - more years than I would care to admit - I spent eight years in the Army as a 98G Voice Intercept Operator, which is a long title for someone that spends a lot of time listening to what other people are saying, taking notes, and then telling someone else what was being said. I won't go into any more details about what I did for a living, but for several years I was stationed in Fulda, Germany, where I was a member of the 511th Military Intelligence Company, which was attached to the 11th Armored Cavalry Regiment.
My fellow soldiers and I spent a lot of time hiding in the forests along what was then the border between East and West Germany, which is where the conditions were generally the best for our line of work. During the day we used an AN/TRQ-32(V) Radio Receiving Set, which we affectionately called the "Turkey 32."
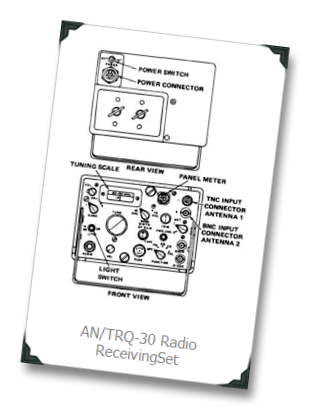
The Turkey 32 was my favorite piece of equipment, and it's primarily used for direction finding operations. (Which means "locating the bad guys.") The only trouble with the Turkey 32 was - it used a great deal of fuel, and its generator was horribly loud, so at night we would shut down the Turkey 32 and use our AN/TRQ-30 Manpack Radio Receiving Set to continue our listening activities... which we called the "Turkey 30."
These radios were left over from a bygone era in the distant past - like the Korean War, or maybe the Civil War - so they were really starting to show their age. One of our radios was falling apart - literally. The knobs on the face panel kept falling off, the reception was terrible, the tuner barely moved, etc. I knew that my Turkey 30 was on its last legs and was in dire need of some kind of emergency maintenance, so one day I hauled my Turkey 30 to our Circuits & Electronics (C&E) office to see what my options were. (I was secretly hoping that C&E would replace the radio, but I was almost certain that it would simply spend a few weeks in the shop for repairs.) I had a good friend who was working in C&E that day, SP4 Villarreal, and he replied that as long as the radio was working, there was nothing that he could do about it.
So I started to pack up the radio, and I was probably muttering something about the fact that I had no idea how long it would take for the radio to eventually die, when Villarreal stopped me and said, "Perhaps you weren't paying attention, so listen to me very closely this time - we can't fix it, but if it doesn't work then we can replace it."
And suddenly - the light bulb turned on.
I blissfully carried the Turkey 30 back to our platoon office in the 511th building and announced to everyone, "Gentlemen, this radio has to die - today." So we spent the next hour or so having a contest to see who could throw the Turkey 30 the furthest from the 2nd-story window where our platoon office was located. After everyone had made their share of attempts at breaking the previous distance record, we declared the contest winners with the usual pomp and circumstance that is called for in such occasions - which means that several people were undoubtedly punched a few times before heading back to work.
Once that was taken care of, I packed up the Turkey 30 and strolled back to the C&E office, where I announced to Villarreal that, "For some reason my Turkey 30 has stopped working." Villarreal didn't blink as he overlooked the massive dents and broken glass and replied, "Well, we'll just have to order you a replacement."
It's times like that when it's great to have friends in the right places. ![]()