Error: Class Not Registered (0x80040154) when Querying FTP Runtime State
29 June 2012 • by Bob • FTP, IIS
I had a great question from a customer earlier today, and I thought that it was worth blogging about. The problem that he was running into was that he was seeing the following error when he was trying to query the runtime state for the FTP service in an application that he was writing:
Class not registered (Exception from HRESULT: 0x80040154 (REGDB_E_CLASSNOTREG))
He was using Visual Basic, and his code looked okay to me, so for the moment I was stumped.
I'm more of a C# guy, and I remembered that I had written the following blog many years ago:
Viewing current FTP7 sessions using C#
I copied the code from that blog into a new Visual Studio project, and I got the same error that he was seeing when I ran my code - this had me a little more confused. Have you ever said to yourself, "Darn - I know that worked the other day...?" ;-]
I knew that there is more than one way to access the runtime state, so I rewrote my sample application using two different approaches:
Method #1:
AppHostAdminManager objAdminManager = new AppHostAdminManager(); IAppHostElement objSitesElement = objAdminManager.GetAdminSection("system.applicationHost/sites", "MACHINE/WEBROOT/APPHOST"); uint intSiteCount = objSitesElement.Collection.Count; for (int intSite = 0; intSite < intSiteCount; ++intSite) { IAppHostElement objFtpSite = objSitesElement.Collection[intSite]; Console.WriteLine("Name: " + objFtpSite.Properties["name"].StringValue); IAppHostElement objFtpSiteElement = objFtpSite.ChildElements["ftpServer"]; IAppHostPropertyCollection objProperties = objFtpSiteElement.Properties; try { IAppHostProperty objState = objProperties["state"]; string ftpState = objState.StringValue; Console.WriteLine("State: " + ftpState); } catch (System.Exception ex) { Console.WriteLine("\r\nError: {0}", ex.Message); } }
Method #2:
ServerManager manager = new ServerManager(); foreach (Site site in manager.Sites) { Console.WriteLine("Name: " + site.Name); ConfigurationElement ftpServer = site.GetChildElement("ftpServer"); try { foreach (ConfigurationAttribute attrib in ftpServer.Attributes) { Console.WriteLine(attrib.Name + ": " + attrib.Value); } } catch (System.Exception ex) { Console.WriteLine("\r\nError: {0}", ex.Message); } }
Both of these methods returned the same COM error, so this was getting weird for me. Hmm...
The FTP runtime state is exposed through a COM interface, and that is implemented in a DLL that is named "ftpconfigext.dll". That file should be registered when you install IIS, and I re-registered it on my system just for good measure, but that didn't resolve the issue.
I had a brief conversation with one of my coworkers, Eok Kim, about the error that I was seeing. He also suggested re-registering the DLL, but something else that he said about searching the registry for the InprocServer32 entry made me wonder if the whole problem was related to the bitness of my application.
To make a long story short - that was the whole problem.
Both the customer and I were creating 32-bit .NET applications, and the COM interface for the FTP runtime state is implemented in a 64-bit-only DLL. Once we both changed our projects to compile for 64-bit platforms, we were both able to get the code to run. (Coincidentally, all I had was a 32-bit system when I wrote my original blog, so I probably would have run into this sooner if I had owned a 64-bit system way back then. ;-])
Note: This blog was originally posted at http://blogs.msdn.com/robert_mcmurray/
Microsoft IIS 8.0 Express Release Candidate is Released!
31 May 2012 • by Bob • IIS Express
In addition to all of the other great products that Microsoft has released today, I’m happy to announce the release of the Internet Information Services (IIS) 8.0 Express Release Candidate. You can install the IIS 8.0 Express Release Candidate through the Microsoft Download Center by using the following URL:
http://go.microsoft.com/fwlink/?LinkId=254247
IIS 8.0 Express Release Candidate supports the following new features:
- X64 Support
- IIS 8.0 Express supports both 32-bit and 64-bit architectures.
- Shared Features with IIS 8.0
- IIS 8.0 Express shares a great number of features with the full version of IIS; for example, IIS 8.0 Express uses many of the same binaries, configuration files, and error codes as the full version of IIS, so migrating projects between your development environment and your production environment should be easier than ever.
- Changing the User Home Directory
- IIS 8.0 Express supports changing the user's home directory, which is mapped to the %IIS_USER_HOME% variable in configuration. By default this path is located at %UserProfile%\Documents\IISExpress, but users can change this by setting a CustomUserHome registry property in HKCU\Software\Microsoft\IISExpress, or by specifying the "/userhome" parameter when launching iisexpress.exe.
- WebSocket Support
- IIS 8.0 Express supports writing WebSocket applications. For more information, see the WebSocket protocol specification or the System.Net.WebSockets Namespace topic on Microsoft's MSDN website.
- AppCmd Support for editing multiple configuration files
- The AppCmd utility now supports a "/AppHostConfig" parameter, which makes it possible to use AppCmd to edit multiple ApplicationHost.config files and not just the primary configuration file.
For more information, see the IIS 8.0 Express ReadMe file.
My thanks to Eok Kim, Jeong Hwan Kim, Yamini Jagadeesan, Wade Hilmo, and Won Yoo!
Note: This blog was originally posted at http://blogs.msdn.com/robert_mcmurray/
Extensibility Updates in the FTP 8.0 Service
20 April 2012 • by Bob • IIS, FTP, Extensibility
A few years ago I wrote a blog that was titled "FTP 7.5 Service Extensibility References", in which I discussed the extensibility APIs that we added in FTP 7.5. Over the next couple of years I followed that initial blog with a series of walkthroughs on IIS.net and several related blog posts. Here are just a few examples:
- How to use Managed Code (C#) to create an FTP Home Directory Provider that is based on the Remote Client IP Address
- How to Use Managed Code (C#) to Create an FTP Home Directory Provider for the Days of the Week
- FTP and LDAP - How to Use Managed Code (C#) to Create an FTP Authentication Provider that uses an LDAP Server
- How to Create an Authentication Provider for FTP 7.5 using BlogEngine.NET's XML Membership Files
- Merging FTP Extensibility Walkthroughs - Part 1
- Merging FTP Extensibility Walkthroughs - Part 2
- Automatically Creating Checksum Files for FTP Uploads
- Changing the Identity of the FTP 7 Extensibility Process
- etc.
In today's blog I'd like to discuss some of the extensibility features that we added in FTP 8.0, and show you how you can use those in your FTP providers.
Custom FTP Authorization
In FTP 7.5 we provided interfaces for IFtpAuthenticationProvider and IFtpRoleProvider, which respectively allowed developers to create FTP providers that performed user and role lookups. In FTP 8.0 we added a logical extension to that API set with IFtpAuthorizationProvider interface, which allows developers to create FTP providers that perform authorization tasks.
With that in mind, I wrote the following walkthrough on the IIS.net web site:
The title pretty much says it all: the provider that I describe in that walkthrough will walk you through the steps that are required to create an FTP provider that provides custom user authentication, verification of role memberships, and authorization lookups on a per-path basis.
Custom FTP Event Handling
In FTP 7.5 if you wanted your provider to respond to specific user activity, the best way to do so was to implement the IFtpLogProvider.Log() interface and use that to provide a form of pseudo-event handling. In FTP 8.0 we add two event handling interfaces, IFtpPreprocessProvider and IFtpPostprocessProvider, which respectively allow developers to write providers that implement functionality before or after events have occurred.
With that in mind, I wrote the following walkthrough on the IIS.net web site:
Once again, the title says it all: the provider that I describe in that walkthrough will walk you through the steps that are required to create an FTP provider that prevents FTP clients from downloading more files per-session than you have allowed in your configuration settings.
Happy coding!
Note: This blog was originally posted at http://blogs.msdn.com/robert_mcmurray/
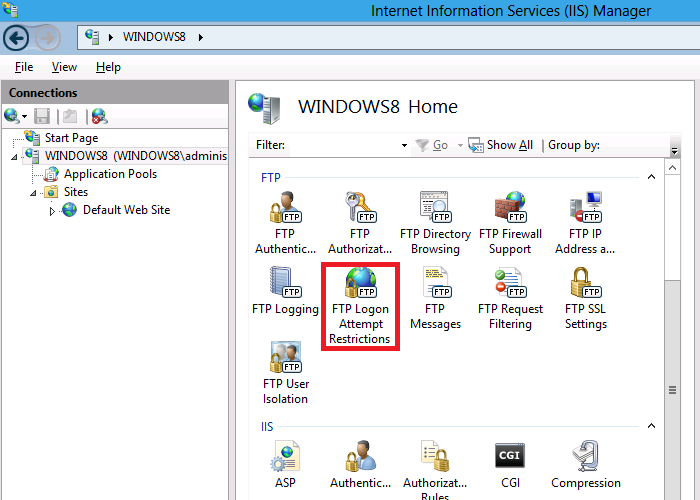
FTP Logon Restrictions in IIS 8
19 March 2012 • by Bob • FTP, IIS
One of the biggest asks from our customers over the years was to provide a way to prevent brute-force password attacks on the FTP service. On several of the FTP sites that I host, I used to see a large number of fraudulent logon requests from hackers that were trying to guess a username/password combination. My first step in trying to prevent these kinds of attacks, like most good administrators, was to implement strong password requirements and password lockout policies. This was a good first step, but there is an unfortunate downside to password lockout policies - once a hacker locks out a user account, that means that a valid user is locked out of their account. What's more, a hacker can continue your server.
The FTP service has had a feature to block IP addresses, but this required something of a manual process to discover malicious behavior. To accomplish this, you had to query your log files for excessive activity, and then added the IP addresses from potential hackers to your blacklist of banned IP addresses. Besides the manual nature of this process, another big drawback to this approach is the fact that it isn't real-time, so a malicious client could be attacking your system for some time before you discover their activity.
With that in mind, my next step was to go after the hackers and block their IP addresses from accessing my server. To that end, I created the custom authentication provider for the FTP 7.5 service that I documented in the following walkthrough:
How to Use Managed Code (C#) to Create an FTP Authentication Provider with Dynamic IP Restrictions
That was pretty effective, but it was really intended to be a stop-gap measure while we were working on a built-in feature for the FTP service that ships with IIS 8, which allows you to block malicious logon attempts.
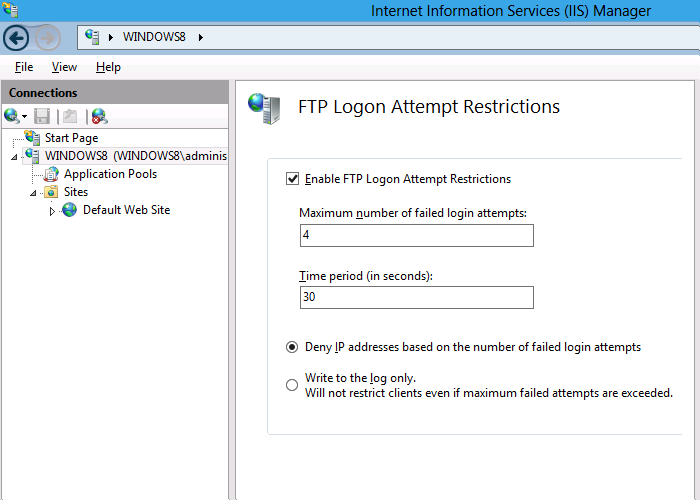
Here's the way this feature works - at the server level, you configure the maximum number of failed logon attempts that you will allow within a given time period; if someone fails to logon within that time frame, the FTP service will drop the connection, and the client will be blocked from accessing your server until the time frame has passed.
Additional details are available in the walkthrough that I wrote at the following URL:
IIS 8.0 FTP Logon Attempt Restrictions
If you'd like to try out the new FTP Logon Restrictions feature, you can download the Windows Server 8 Beta from the following URL:
http://www.microsoft.com/en-us/server-cloud/windows-server/v8-default.aspx
Note: This blog was originally posted at http://blogs.msdn.com/robert_mcmurray/